Sponsored By
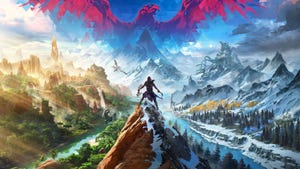
A zombie in Dead Island 2.
Business
Dead Island 2 shambles to 7 million players in over a yearDead Island 2 shambles to 7 million players in over a year
The island may be dead, but the player base sure ain't.
Daily news, dev blogs, and stories from Game Developer straight to your inbox